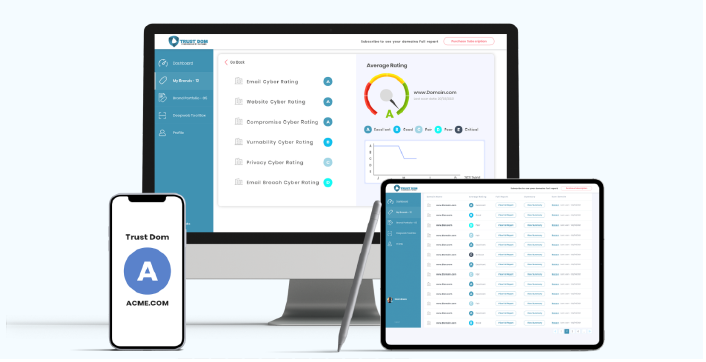
Cygienic Attack Surface Management Services Powered by Cygienic UCRM™ Platform
Attack Surface Management Service meticulously monitors your digital landscape, identifying and mitigating potential vulnerabilities before they can be exploited.
Attack Surface Management
Testing within the attack surface management service evaluates Email Security, Web Security, Vulnerabilities, Compromised Sites, Data Privacy, and Open Ports to identify and mitigate risks across external internet-facing systems.
- Email Security – Assesses exposure to phishing, spoofing, and misconfigured email protections.
- Web Security – Tests websites & applications for misconfigurations or insecure protocols.
- Vulnerabilities – Identifies known software flaws and unpatched systems that attackers could exploit.
- Compromised Sites – Detects signs of domains or assets already flagged as breached or malicious.
- Data Privacy – Checks for exposed sensitive data, leaks, or weak data protection practices.
- Open Ports – Scans for unnecessary or insecure ports that could provide unauthorized access paths.
Cygienic's Attack Surface Management service follows a well-structured process, from client onboarding to remediation advisory reports, to ensure comprehensive cybersecurity. The stages can be summarized as follows:
- Client Onboarding: The process begins with client onboarding, where Cygienic collaborates closely with your organization to gather essential information about your web-facing servers, digital assets, and specific concerns.
- Discovery and Assessment: The next step involves UCRM to perform a comprehensive scan of your external web-facing servers. Cygienic utilizes advanced algorithms to search the surface for potential vulnerabilities and threat indicators. This in-depth assessment uncovers potential risks and weaknesses.
- Threat Identification: Once the initial assessment is complete, Cygienic identifies potential threats and vulnerabilities within your digital perimeter. Our experts analyze the data to differentiate genuine risks from false positives, ensuring that the focus remains on critical issues that require attention.
- Remediation Recommendations: After pinpointing vulnerabilities, Cygienic generates detailed remediation recommendations.
- Ongoing Monitoring Via UCRM: We continue to monitor your external web-facing servers to ensure the effectiveness of implemented measures. This ongoing vigilance is critical in identifying and addressing new threats that may emerge.
- Periodic Advisory Reports: Cygienic UCRM platform provides regular advisory reports summarizing the status of your attack surface management. These reports offer insights into the current threat landscape, the progress of remediation efforts, and recommendations for further security enhancements. Our advisory reports keep you informed and guide you in maintaining a robust cybersecurity posture.
Cygienic's Attack Surface Management service offers a holistic approach to safeguarding your organization's digital assets. From the initial client onboarding to the ongoing monitoring and advisory reports, we ensure that your cybersecurity remains resilient and responsive to evolving threats.
Download Our Attack Surface Management Brochure
Contact sales@cygienic.com