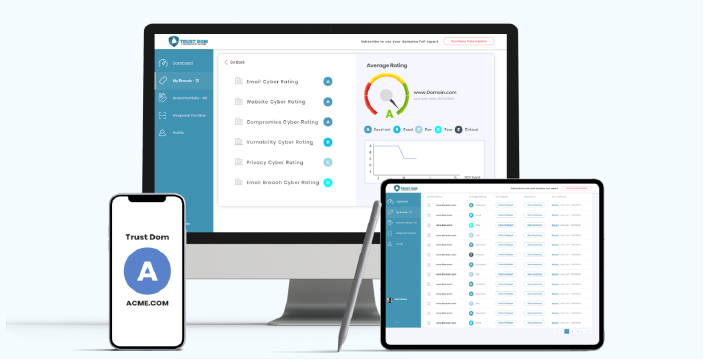
Cygienic UCRM Platform
Unified Cyber Risk Manager
Everything you need in one seamless platform. No cyber expertise required, no installation, no hassle - platform and cyber analyst training included.
Cygienic UCRM is a SaaS solution offering management of an organization’s cyber risks. It maps all components and assets within your cybersecurity ecosystem, including attack surface data, threat intelligence, compliance, and third-party risks, providing a comprehensive risk profile and cyber analytics report for IT and business owners to understand.
Our budget-friendly UCRM licensing model is based on your budget needs - from Startup to enterprise plans, we can offer unbeatable value in both price and service.
All administrator licenses include full onboarding support through the Cygienic platform. This comes with:
This onboarding package is designed to give administrators the confidence and tools they need to get up and running efficiently, while ensuring long-term success on the Cygienic platform.
Evaluate your business’s financial exposure to cyberattacks with our advanced risk assessment tools. Gain critical insights to quantify potential losses and strengthen your cybersecurity strategy.
Cost Impact Insurance Calculator and adjustable formula modules:
From industry regulations and standard questionnaires to security policies and awareness material, the platform has everything pre-built and centrally managed for you.
Executive summary reports designed for board-level presentations, facilitating a clear understanding of the company's risk profile. Receive a high-level recommendation report for framework controls and policies, including policy documents, tech guides, playbooks, and security awareness training samples, supported by insights from previous stages.
A non-intrusive cybersecurity assessment of your company's internet-facing assets, including web servers, applications, websites, and email systems. This evaluation reviews security settings and identifies potential vulnerabilities, providing a comprehensive cybersecurity rating and remediation recommendations.
Industry-standard tools scan your company systems for vulnerabilities, search the darkweb for company confidential data leaks, and check if company systems have been compromised.
Cybersecurity analyst training on the Cygienic UCRM™ platform equips professionals with the practical skills and tools needed to detect, monitor, and mitigate cyber risks across diverse business environments. Delivered through Cygienic’s Unified Cyber Risk Manager (UCRM™), the programme blends real-world scenarios with advanced platform features to give analysts hands-on experience in managing security posture, compliance, and executive reporting. By the end of the training, participants will be able to confidently monitor and communicate cyber risks while aligning with business and regulatory priorities.
Key training modules include:
Visit Cybersecurity Analyst Training Webpage